OSDP: Why Wiegand Is Dead and What Replaces It
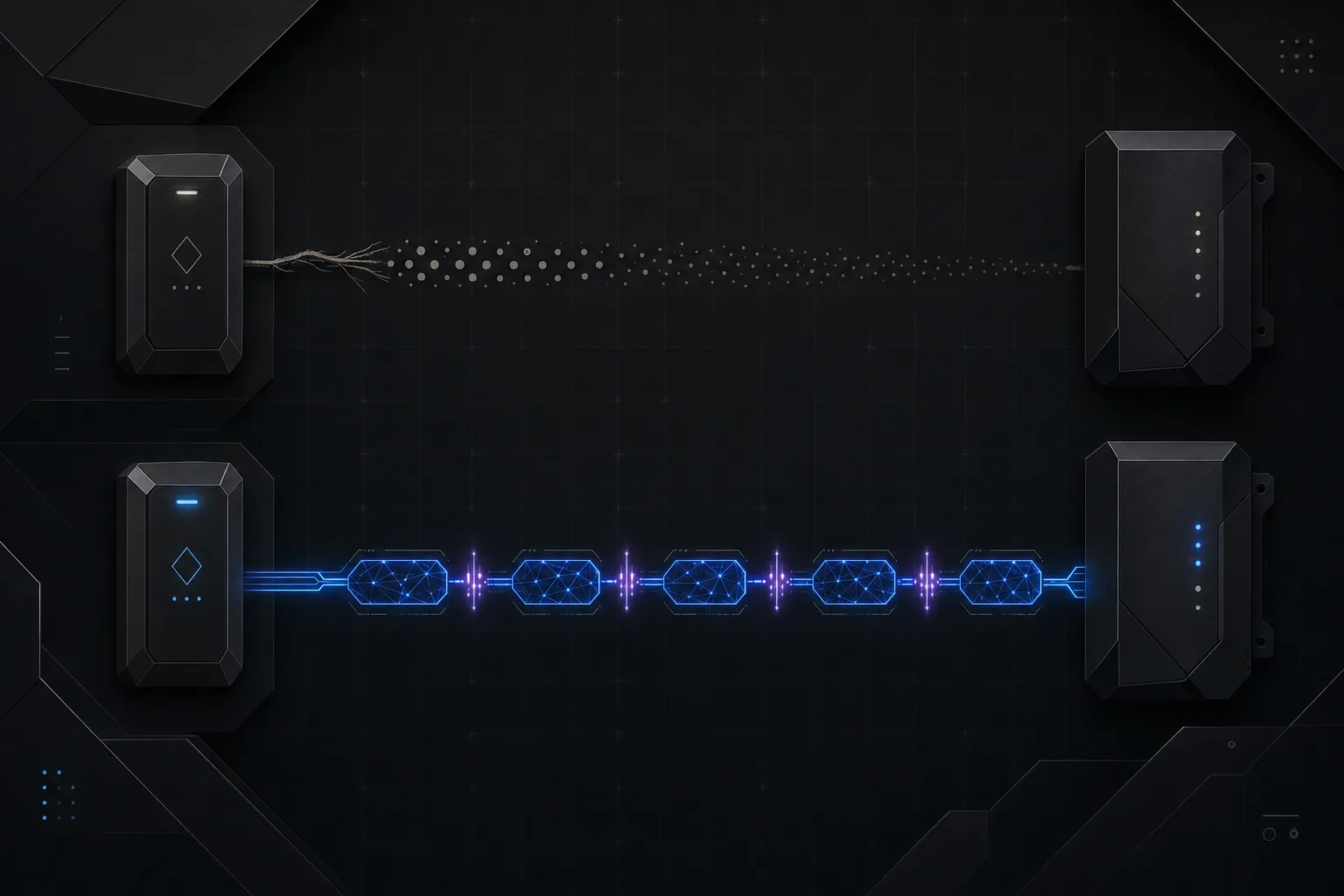
For over four decades, the Wiegand protocol has been the default communication link between access control readers and panels. It was a reasonable choice in 1980. It is an indefensible one today. Wiegand transmits credentials in plaintext over unshielded, unmonitored wires with no encryption, no authentication, and no way to know if someone has tapped the line or ripped the reader off the wall. Every serious access control vulnerability exploited in the last decade, from long-range credential sniffing to reader substitution attacks, traces back to the fundamental architectural failures of Wiegand.
The Security Industry Association (SIA) recognized this problem over a decade ago and developed the Open Supervised Device Protocol (OSDP) as a modern replacement. OSDP v2, ratified as an IEC standard (IEC 60839-11-5), delivers AES-128 encrypted, bidirectional communication over RS-485 multi-drop wiring. It is not merely an incremental improvement. It is a complete rearchitecture of how readers and panels communicate, and it eliminates entire categories of attack that Wiegand makes trivially easy.
The Fundamental Flaws of Wiegand
Understanding why Wiegand must be replaced requires understanding exactly how it fails. The protocol uses two signal wires, DATA0 and DATA1, each of which pulses low for approximately 50 microseconds to represent a binary zero or one. There is no clock signal, no handshake, no acknowledgment, and no encryption. The reader sends a fixed-length bit string (typically 26-bit standard Wiegand, though 34-bit and 37-bit variants exist) to the panel, and that is the end of the conversation.
- No encryption whatsoever. Credential data travels as plaintext electrical pulses. Anyone with a $15 microcontroller and two alligator clips can intercept and replay a valid credential. Tools like the ESPKey and BLEKey were purpose-built to exploit this, and they work on virtually every Wiegand installation in the world.
- Unidirectional communication. Data flows only from reader to panel. The panel cannot send commands back to the reader to update firmware, change LED behavior, display messages on an OLED screen, or verify reader integrity. The reader is a dumb transmitter.
- No tamper supervision. If an attacker removes the reader from the wall, cuts the wires, or substitutes a rogue reader, the panel has no protocol-level mechanism to detect the change. Some panels monitor a separate tamper switch, but this is an out-of-band hack, not an inherent protocol feature.
- Fixed bit-length limitations. Standard 26-bit Wiegand supports only 255 facility codes and 65,535 card numbers. Large enterprises routinely encounter duplicate credentials when sourcing cards from multiple vendors. Extended formats (Corporate 1000, H10304) help but introduce interoperability headaches.
- Distance limitations. Wiegand's unbalanced signaling degrades rapidly over distance. The practical maximum is 150 meters (500 feet) over 18 AWG wire, and signal integrity problems begin well before that threshold in electrically noisy environments.
The ESPKey Attack in 30 Seconds
An attacker walks up to any exterior Wiegand reader, removes the cover (usually held by two Torx screws), clips a device the size of a postage stamp onto the DATA0 and DATA1 wires, replaces the cover, and walks away. Every credential presented to that reader is now logged and can be replayed at will. The entire attack takes under 60 seconds and leaves no visible evidence. This is not theoretical; it is demonstrated at every major security conference and works on nearly every Wiegand installation worldwide.
OSDP v2: Architecture and Security Model
OSDP operates over RS-485, a balanced differential signaling standard that supports multi-drop topologies and cable runs up to 1,200 meters (4,000 feet) on a single twisted pair. RS-485 is inherently more robust than Wiegand's single-ended signaling, with superior noise immunity and the ability to daisy-chain up to 8 readers on a single two-wire bus (though 4 per run is the practical recommendation for security installations).
The protocol implements a master-slave polling architecture where the access control panel (master) sequentially polls each reader (slave) at addresses 0 through 126. Each reader responds with credential data, tamper status, and diagnostic information. This bidirectional communication is the foundation for every security improvement OSDP delivers over Wiegand.
OSDP v2's Secure Channel Protocol (SCP) establishes an AES-128 encrypted session between the panel and each reader. The process begins with a mutual authentication handshake where both devices prove they possess the correct base key. A session key is then derived, and all subsequent communication is encrypted and authenticated with a message authentication code (MAC). If an attacker taps the RS-485 bus, they capture only ciphertext. If they substitute a rogue reader, the authentication handshake fails and the panel immediately flags the compromise.
Bidirectional Communication: Beyond Credentials
The downstream channel from panel to reader unlocks capabilities that Wiegand physically cannot support. OSDP-compliant panels can push firmware updates to readers over the same RS-485 bus used for credential exchange, eliminating the need to physically visit every reader for updates. Panels can control reader LEDs and buzzers to provide visual and audible feedback (lockdown indication, maintenance mode, custom access granted/denied patterns). Readers with displays can show text messages pushed from the panel. Biometric templates can be loaded and managed centrally. All of this happens over the same two-wire connection.
Supervised wiring is another critical advantage. The panel continuously polls each reader. If a reader fails to respond within the configured timeout, the panel generates a supervision alarm. This means a severed cable, a powered-down reader, or a removed reader is detected in seconds rather than discovered during the next physical inspection (which, in many organizations, is never).
Wiegand vs. OSDP: Complete Comparison
| Attribute | Wiegand | OSDP v2 |
|---|---|---|
| Encryption | None (plaintext) | AES-128 with SCP |
| Communication | Unidirectional (reader to panel) | Bidirectional |
| Tamper Detection | Out-of-band only (separate switch) | In-band supervision polling |
| Max Cable Distance | 150 m (500 ft) on 18 AWG | 1,200 m (4,000 ft) on RS-485 |
| Topology | Home run (1 reader per cable) | Daisy-chain multi-drop (up to 8) |
| Firmware Updates | Requires physical visit | Over the wire (file transfer) |
| Credential Capacity | 26-37 bits typical | Unlimited (variable length) |
| Biometric Support | Not possible | Native template transfer |
| Smart Card Support | Reader decodes, sends bits | Transparent card data to panel |
| Wiring Cost (per reader) | Dedicated home run required | Shared bus reduces cable runs 40-60% |
Migration Strategies: Wiegand to OSDP
Replacing every reader and re-pulling every cable in a large enterprise is rarely practical as a single project. Fortunately, OSDP migration can be staged. Most modern access control panels from manufacturers like HID, Mercury (now Genetec), Axis, and AMAG already support OSDP natively or via a firmware update. The transition typically focuses on the reader side and the wiring.
- Dual-technology readers. Many current readers (HID Signo, ASSA ABLOY pivCLASS) support both Wiegand and OSDP on the same hardware. You can install these readers using existing Wiegand wiring and switch to OSDP later when the panel firmware is updated and RS-485 wiring is run.
- Wiegand-to-OSDP conversion modules. Devices like the Cypress OSDP Converter sit between a legacy Wiegand reader and an OSDP-capable panel, translating Wiegand bit strings into OSDP packets. This does not add encryption at the reader-to-converter segment, but it allows a phased approach where converters provide OSDP supervision and panel-side encryption while readers are replaced over time.
- Daisy-chain wiring savings. When running new cable for OSDP, take advantage of the multi-drop topology. A single RS-485 bus from the panel can serve up to 4 readers in a daisy-chain, dramatically reducing cable runs. Use shielded twisted pair (Belden 9842 or equivalent) rated for RS-485 applications. This wiring reduction often offsets 40-60% of the reader upgrade cost.
- Prioritize high-risk doors first. Begin OSDP migration at exterior doors, data centers, executive suites, and any door where credential interception would have the highest impact. Interior low-security doors can remain on Wiegand temporarily with an understood and documented risk acceptance.
SIA OSDP Verified Program and Emerging Standards
The SIA OSDP Verified program provides third-party conformance testing to ensure that products claiming OSDP compliance actually implement the protocol correctly. This matters because early OSDP implementations from some manufacturers were incomplete or incompatible, leading to interoperability problems that gave the protocol an undeserved reputation for being difficult. Always specify OSDP Verified products in your designs. The SIA maintains a public registry of verified products on their website.
Looking ahead, OSDP over IP is an emerging extension that encapsulates OSDP packets in TCP/IP for transport over Ethernet networks. This is particularly relevant for distributed campus environments where readers are far from panels and IP infrastructure already exists. While not yet widely deployed, several manufacturers are developing OSDP-over-IP implementations that promise to further simplify wiring while maintaining the protocol's encryption and supervision capabilities.
Specifier's Note on Secure Channel
Not all OSDP implementations enable Secure Channel by default. Some manufacturers ship readers with SCP disabled to simplify commissioning, which means the connection is OSDP but unencrypted. Always verify that Secure Channel is explicitly enabled in both the reader configuration and the panel software. An OSDP link without SCP is better than Wiegand (you still get supervision and bidirectional communication) but it does not provide the encryption that is the protocol's primary security advantage.
The Bottom Line
Every Wiegand installation is a known, exploitable vulnerability. The tools to attack it are cheap, widely available, and require no specialized skill. OSDP v2 with Secure Channel eliminates the credential interception attack entirely, adds tamper supervision, enables centralized reader management, and reduces wiring costs through multi-drop topology. The protocol is an IEC international standard, supported by every major access control manufacturer, and verified through the SIA's conformance testing program. There is no technical, financial, or operational argument for specifying Wiegand in new construction, and there is a strong case for accelerating the migration of existing installations.
Zimy Electronics designs and deploys OSDP-based access control systems for commercial, industrial, and government clients. Zimy Electronics has migrated hundreds of doors from legacy Wiegand to OSDP v2 Secure Channel, using phased approaches that minimize disruption and maximize the return on existing panel investments. Whether you are specifying a new access control system or planning a Wiegand migration, we bring the protocol-level expertise to ensure your installation is secure, supervised, and future-ready.